Trends collectively suggest that TF risk is becoming more diffuse, networked and embedded in legitimate global flows, requiring intelligence?driven, multi?sectoral responses rather than reliance on static typology checklists.

By Lt Col Ujjual Abhishek Jha, Retd
Comprehending Terrorist Financing (TF) origins requires an analytical thinking beyond conventional Anti-Money Laundering (AML) framework. Money Laundering (ML) is circular process wherein illicitly acquired money is integrated back to legitimate economy. TF is a linear process wherein source of money can be legal or illegal and is aimed towards a violent action. This differentiation is very important in TF, as it makes detection of TF extremely difficult (no Red Flags, source legal or intent and end point not established). Terrorist financing (TF) are finances that enable terrorist activities. TF differs from typical money laundering in three important ways, origin of funds may be legitimate, amounts involved can be relatively small and primary objective is to ensure funds reach operatives. ?? ????? ?? ??????????? ?? ??????? ??? ??????????? ???? ???? ??????????? ?? ??????. Four stage frameworks of TF model are ??????????, ????, ???????? ??? ?????.
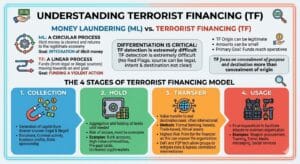
Four Stage Framework TF Model
- Stage 1: Collection. The generation of capital from a diverse source (both legal and illegal/ criminal) to support organization’s expenditures or specific operations. Can be donations, criminal activity, business profits or state sponsored.
- Stage 2: Hold. The aggregation and holding of funds until they are required for an operational need. This stage has the risk of seizure and needs to overcome the same. Can be in bank accounts, high-value commodities, pre-paid cards or un-hosted crypto-wallets.
- Stage 3: Transfer. The transfer of value from the storage point to the end destination or user, often across international borders i.e. transfer of value from holding point to end destination or user. Formal banking, Informal Value Transfer System (Hawala), trade-based or virtual assets are few examples of the same. This stage is often said to be the point of highest risk for the financier as this can expose the organisation. However, the evolution of decentralised finance (DeFi) and peer-to-peer (P2P) technologies has increasingly allowed groups to mitigate these risks by bypassing centralized intermediaries.
- Stage 4: Usage. The final expenditure of funds to facilitate attacks or maintain the organization’s long-term sustainability. Can be for weapon procurement, training, travel, media messaging or social services.
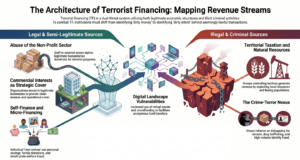
Typology of Sources of Terrorist Financing
TF: Legal & Semi-Legitimate Sources
A substantial portion of TF is resultant of legitimate economic activity, which presents a distinct challenge for financial institutions. If funds originate from a lawful activity and do not stain of criminal predicate, then it necessitates a shift from identifying dirty money to dirty intent. The means are discussed below.
Abuse of the Non-Profit Sector (NPOs) – NPOs and charities have been identified by the FATF as particularly vulnerable to abuse for terrorist financing. E.g. fund diversion of legitimate donations for humanitarian purposes are siphoned off by complicit staff or external actors.
Commercial Interests and Legitimate Businesses – Large terrorist organizations often act as venture capitalists, investing surplus capital into legitimate commercial sectors to ensure a steady stream of income, serving dual purpose, provide a clean revenue stream and offer cover for operatives stay and move.
Self-Finance and the Lone Wolf – The individual operatives have own legitimate income as the primary source of funding. It is often supplemented by micro-financing strategies like welfare and benefit fraud, small loans and personal savings & family donations.
TF: Illegal & Criminal Sources
Industries and Territorial Taxation – For groups that control territory, such as ISIS at its zenith, the primary source of revenue is the exploitation of natural resources and the taxation of the local population.
Kidnapping for Ransom (KFR) – Kidnapping for ransom has become a principal revenue generation source for groups like Al-Qaeda in the Islamic Maghreb (AQIM) and even in the case of ISIS provinces in West Africa, Khorasan, and South Africa.
Drug Trafficking – The intersection of drug trafficking and terrorism is one of the most known aspects of the crime-terror nexus. The reported Taliban’s dependance on the opium trade and Hezbollah’s said involvement in the cocaine trade from South America to Europe show exploitation of drug market by these groups to fund their political projects.
Fraud and Identity Theft – In Western countries terror cells involves in low level but high-volume frauds supporting terrorist financing methods.
Digital Landscape – Introduced new vulnerabilities into FT leading to increased abuse of digital platforms (virtual assets, crowdfunding and social media) to facilitate collection and transfer of funds with speed and anonymity.
Move Typology: Mechanics of Transfer
Post raising and storing of funds, movement of funds is required for operations/ sustenance. The terror outfits mostly employ hybrid method of fund transfer, formal, informal and trade-based systems to evade surveillance.
Formal Fund Transfer – In spite of exhaustive regulation, the formal banking sector remains a primary target for misuse, using individuals with clean backgrounds (straw men) for opening accounts and transactions. Usage of shell companies is also common method to mask the movement of funds. A common method in the formal sector is structuring or smurfing, where large sums is broken into small transactions to avoid trigger of Suspicious Transaction Reports (STRs).
Hawala and Informal Value Transfer Systems (IVTS) – Hawala is an ancient system of value transfer that operates outside the conventional banking sector. It is based on a network of brokers (hawaladars) who facilitate transfers through trust and net settlement rather than the physical movement of money. The characteristics of Hawala as speed, lower costs and potential anonymity, makes it highly attractive for both legitimate remittances and illicit financing. Hawala settlement in often through Reverse Hawala or Bilateral Settlement, where hawaladars balance their accounts by paying for each other’s expenses in or through the invoicing of legitimate trade.
Trade-Based Money Laundering and Terrorist Financing (TBML/TBTF) – TBML is defined as the process of disguising the proceeds of crime and moving value through the use of trade transactions to legitimize their origins. It is one of the most complex methods of value transfer. Mechanisms of TBML include Over and Under-Invoicing, Phantom Shipments (documents generated for goods that are never shipped), Multiple Invoicing and Surrogate Shopping/ Daigou (high purchase of goods using illicit cash and collecting clean money from end-users). As per FATF, TBML is increasingly attractive and is frequently used by groups like Hezbollah and the Taliban, who have established deep connections with international trade and transport companies.
Digital Frontier & Emerging Technologies
The rapid evolution of financial technology has introduced new vulnerabilities into the FT landscape. Terrorists are increasingly misusing digital platforms including virtual assets, crowdfunding and social media, to generate and move funds with unprecedented speed and anonymity.
Virtual Assets (VAs) and Cryptocurrencies – Virtual assets are characterized by non-face-to-face relationships and can permit anonymous funding. While Bitcoin was the initial currency of choice, the transparency of its blockchain has led to a shift toward more privacy-centric and stable assets. The overall VA use in terrorist financing remains relatively lower than cash and Hawala, but its reportedly growing in South and Central Asia.
Crowdfunding and Social Media Integration – Social media platforms as Facebook and Twitter act as broadcast mechanisms to ask donations. Once a potential donor is identified, the conversation moves to private, often encrypted, as Telegram or WhatsApp. Crowdfunding platforms are misused through campaigns, disguising funds as humanitarian aid for conflict zones, using combination of traditional payment methods and new technologies (Crypto) to avoid detection.

Emerging Threats and AI Factor
FATF Update on TF Risks of 2024 and 2025 highlights surge in activity by young, tech-savvy actors who are radicalized online and employ micro-financing. FATF also warned specific AI risks of not only in the recruitment and radicalization but also in automation of fund operations.
Trends collectively suggest that TF risk is becoming more diffuse, networked and embedded in legitimate global flows, requiring intelligence?driven, multi?sectoral responses rather than reliance on static typology checklists. For corporate security and compliance functions, this means that the “financial footprint” of terrorism often appears as small, routine, sometimes even charitable or community?oriented transactions.
(Lt Col Ujjual Abhishek Jha, Retd is a Certified Data Privacy Professional and Strategic & Geopolitical Advisor with over two decades of experience in intelligence, insider threat management, financial crime investigations, and geopolitical risk analysis, advising on complex security and strategic risks.)
The post Linear Path of Terror: Architecture of Modern Terrorist Financing first appeared on The Frontier Manipur.
Read more / Original news source: https://thefrontiermanipur.com/linear-path-of-terror-architecture-of-modern-terrorist-financing/